How are intrusion detection systems ( IDS ) classified?
IDS are classified into 5 types: Network Intrusion Detection System (NIDS): Network intrusion detection systems (NIDS) are set up at a planned point within the network to examine traffic from all devices on the network.
What’s the difference between host-based and network-based intrusion detection?
The host-based intrusion detection system can detect internal changes (e.g., such as a virus accidentally downloaded by an employee and spreading inside your system), while a network-based IDS will detect malicious packets as they enter your network or unusual behavior on your network such as flooding attacks or protocol-specific attacks.
Which is the best method for IDS detection?
Detection Method of IDS: Signature-based Method: Signature-based IDS detects the attacks on the basis of the specific patterns such as number of bytes or number of 1’s or number of 0’s in the network traffic. It also detects on the basis of the already known malicious instruction sequence that is used by the malware.
How is an intrusion prevention system set up?
Intrusion prevention systems also monitor network packets inbound the system to check the malicious activities involved in it and at once sends the warning notifications. Network intrusion detection systems (NIDS) are set up at a planned point within the network to examine traffic from all devices on the network.
IDS are classified into 5 types: Network Intrusion Detection System (NIDS): Network intrusion detection systems (NIDS) are set up at a planned point within the network to examine traffic from all devices on the network.
The host-based intrusion detection system can detect internal changes (e.g., such as a virus accidentally downloaded by an employee and spreading inside your system), while a network-based IDS will detect malicious packets as they enter your network or unusual behavior on your network such as flooding attacks or protocol-specific attacks.
Intrusion prevention systems also monitor network packets inbound the system to check the malicious activities involved in it and at once sends the warning notifications. Network intrusion detection systems (NIDS) are set up at a planned point within the network to examine traffic from all devices on the network.
Detection Method of IDS: Signature-based Method: Signature-based IDS detects the attacks on the basis of the specific patterns such as number of bytes or number of 1’s or number of 0’s in the network traffic. It also detects on the basis of the already known malicious instruction sequence that is used by the malware.
Anomaly-based detection is the process of comparing definitions of what activity is considered normal against observed events to identify significant deviations. An IDPS using anomaly-based detection has profiles that represent the normal behavior of such things as users, hosts, network connections, or applications.
Anomaly-based: a newer technology designed to detect and adapt to unknown attacks, primarily due to the explosion of malware. This detection method uses machine learning to create a defined model of trustworthy activity, and then compare new behavior against this trust model.
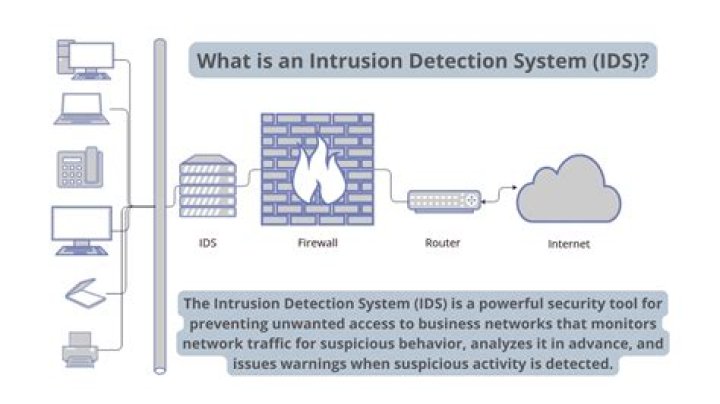
IDS vs Firewalls An IDS is a passive monitoring device that detects potential threats and generates alerts, enabling security operations center (SOC) analysts or incident responders to investigate and respond to the potential incident. An IDS provides no actual protection to the endpoint or network.
There are different types of Intrusion Detection systems based on different approaches. The two main divisions exist between signature based IDSs and behavioral IDSs. There are multiple subcategories depending on the specific implementation. Signature based IDSs, like Snort, function like anti-virus software.
A network monitoring tool with DPI can identify anomalies in network traffic – such as fragmented packets and activity across non-standard ports – to alert network administrators of a potential intrusion, and provide the information required to conduct a thorough investigation.
By using the signature database, IDS ensures quick and effective detection of known anomalies with a low risk of raising false alarms. It analyzes different types of attacks, identifies patterns of malicious content and help the administrators to tune, organize and implement effective controls.
Intrusion detection systems are used to detect anomalies with the aim of catching hackers before they do real damage to a network. They can be either network- or host-based. Intrusion detection systems work by either looking for signatures of known attacks or deviations from normal activity.
The majority of intrusion prevention systems utilize one of three detection methods: signature-based, statistical anomaly-based, and stateful protocol analysis.
The main difference being that firewall performs actions such as blocking and filtering of traffic while an IPS/IDS detects and alert a system administrator or prevent the attack as per configuration. A firewall allows traffic based on a set of rules configured.
Network intrusion detection systems (NIDS) are placed at a strategic point or points within the network to monitor traffic to and from all devices on the network. It performs an analysis of passing traffic on the entire subnet, and matches the traffic that is passed on the subnets to the library of known attacks.
What is active and passive IDS?
An active Intrusion Detection Systems (IDS) is also known as Intrusion Detection and Prevention System (IDPS). A passive IDS is a system that’s configured to only monitor and analyze network traffic activity and alert an operator to potential vulnerabilities and attacks.
Which is better Suricata vs snort?
One of the main benefits of Suricata is that it was developed much more recently than Snort. Fortunately, Suricata supports multithreading out of the box. Snort, however, does not support multithreading. No matter how many cores a CPU contains, only a single core or thread will be used by Snort.
What are the two main types of intrusion detection systems?
The most common classifications are network intrusion detection systems (NIDS) and host-based intrusion detection systems (HIDS). A system that monitors important operating system files is an example of an HIDS, while a system that analyzes incoming network traffic is an example of an NIDS.
What is the drawback of using IDS?
Intrusion detection systems are able to detect behavior that is not normal for average network usage. While it’s good to be able to detect abnormal network usage, the disadvantage is that the intrusion software can create a large number of false alarms.
What is a disadvantages of using an IDS?
The IDS does not stop malicious traffic. The IDS works offline using copies of network traffic. The IDS requires other devices to respond to attacks.
Why do we use IDS?
A network intrusion detection system (NIDS) is crucial for network security because it enables you to detect and respond to malicious traffic. The primary benefit of an intrusion detection system is to ensure IT personnel is notified when an attack or network intrusion might be taking place.
Which is the most secure type of firewall?
Proxy Server Firewalls
Also called the application level gateways, Proxy Server Firewalls are the most secured type of firewalls that effectively protect the network resources by filtering messages at the application layer. Proxy firewalls mask your IP address and limit traffic types.
What are intrusion attacks?
A network intrusion refers to any unauthorized activity on a digital network. Network intrusions often involve stealing valuable network resources and almost always jeopardize the security of networks and/or their data.